Monokee’s Access Management capabilities cater to both internal and external users, addressing use cases across a wide range of applications and services. It offers centralized identity management, single sign-on, multi-factor authentication, and granular authorization controls. These features align with external trends such as the convergence of IAM features, SaaS adoption, passwordless authentication, adaptive access, and cybersecurity mesh.
5 posts tagged with "Monokee 4.x.x"
View All TagsMonokee 4.0 Decentralized Identity
The identity landscape is evolving from well-known identity federations to fully decentralized solutions. The new Decentralized Identity (DCI) paradigm was designed to solve the existing problems with paper-based IDs in the digital realm by shifting the models toward user-centric, trustworthy, and privacy-preserving ones.
Monokee 4.0 Identity Governance and Administration
Monokee offers a potent solution with robust capabilities that are in line with the fundamental IGA functionalities. It provides inherent support for identity lifecycle management, ensuring that users have appropriate access when needed. The access request processes are streamlined, powered by the V.I.O. to further enhance access control and identity management. Monokee also features inherent capabilities for basic analytics and reporting, offering valuable insights into user activity and access patterns.
Monokee 4.0 Identity Orchestration
The term "identity orchestration" has become a popular buzzword, but its broad scope can sometimes lead to confusion. It encompasses a wide range of activities, from streamlining user journeys to integrating complex backend systems. This lack of clear definition can make it difficult for organizations to understand exactly what capabilities fall under this umbrella.
Monokee recognizes this need for disambiguation.
By breaking down identity orchestration into three distinct pillars – user experience, system integration, and enterprise process orchestration – we provide a clearer picture of the specific functionalities encompassed within this concept. This multi-faceted approach allows us to offer our clients targeted solutions that address their unique identity management needs.
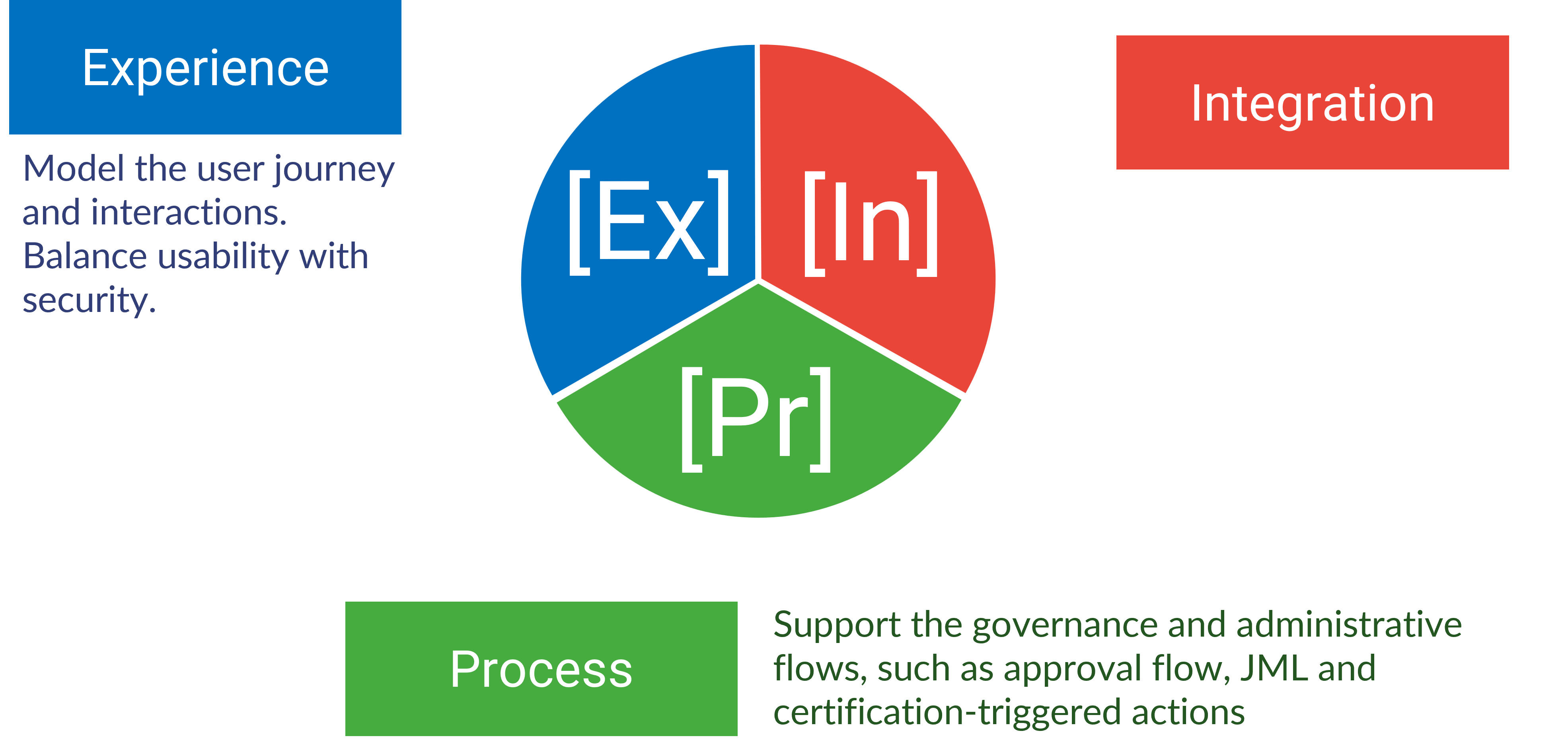
Monokee identifies six enabling technologies for Identity Orchestration: a) User Journey Orchestration, b) Access Management, c) No/Low Code, d) Governance, e) Identity Consolidation, f) Decentralized Identities
Monokee 4.0 Privileged Access Management
Monokee only covers a minimum number of features in Privileged Access Management (PAM) and is designed to cover the requirements of small to medium organizations. For larger ones, Monokee supports full integration with third-party solutions such as CyberArk or Delinea. Monokee currently does not support password vaulting, activities control, in-session monitoring, privilege evaluation, or attestation. For these requirements, integration with a third-party partner is advised.




